Online payments have undoubtedly revolutionized our lives, offering unparalleled convenience in sending money across borders and facilitating global commerce and connectivity.
Among these payment innovations, Peer-to-Peer (P2P) payment apps have emerged as a game-changer, making it easier for individuals to transfer money to friends, family, or merchants seamlessly.
Platforms like Zelle, PayPal, Venmo, and Cash App have become household names, transforming the way people handle financial transactions.
Unraveling the cash conundrum: The sneaky symphony of peer-to-peer payment fraud
As with any technological breakthrough, this convenience comes with its own share of challenges. Recently, cybercriminals have found new targets for their illicit activities – Payment Apps! While some hackers have managed to breach the systems of these companies, most scams involve manipulating users into unknowingly giving away their hard-earned money.
One such notorious case is related to Mobikwik, where individuals fell prey to fraudulent tactics, losing substantial sums of money.
In a specific incident in Bengaluru, two residents reported losing over Rs 50,000 each through phone calls. One of the victims received an Interactive Voice Response (IVR) call claiming unauthorized access to their mobile wallet account.
The fraudulent voice then coerced him into providing the OTP (One-Time Password) to block the account, only to find that Rs 5,000 had been debited the next morning, summing up to Rs 60,000. Similarly, another victim was duped by a fake message concerning non-payment of electricity bills, leading to a loss of Rs 53,545.
Ballad of Cash App swindles: Losing it all!
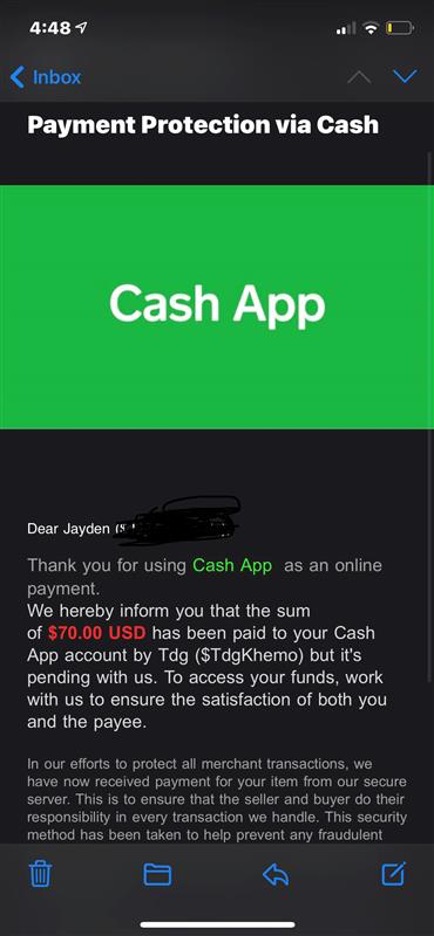
In recent times, the popular payment app Cash App has fallen victim to a wave of hacking attacks, causing unsuspecting users to lose hundreds of dollars.
Reports suggest that hackers are gaining unauthorized access to users’ accounts, transferring money, and leaving victims in despair.
This alarming trend has caught cybersecurity experts’ attention and led to a growing concern about the safety of digital payment platforms like Cash App and Venmo.
One such victim, Liz Shelby, shared her heart-wrenching experience after her son’s savings, intended for a short vacation with his grandmother, vanished from his Cash App account.
Marvis Herring, another unfortunate target, encountered an attempted theft of $1,400 in two separate transactions.
Fortunately, his bank managed to block the fraudulent activities. However, this ordeal highlights the severity of the issue and the urgency for tighter security measures.
The absence of a traditional password for Cash App accounts raises concerns about its vulnerability. Users can create accounts using just an email address or a phone number, and login codes are sent to either upon registration.
This system seems to have become an easy entry point for hackers, who have been seen selling login details of Cash App accounts on dark web marketplaces and fraud websites.

These stolen accounts often contain the login credentials and additional information, such as the victim’s email address and even their cookie files, providing the necessary tools to pose as a legitimate user.
This information allows fraudsters to deceive sites and applications, making unauthorized transactions without raising suspicion.
Poking the veil of multifaceted payment app hacks
Moreover, the hackers’ misuse of compromised accounts extends beyond theft, as it appears they also utilize the platform for money laundering purposes.
By offering newly created and verified accounts on the dark web, these fraudsters enable money transfers without the need for identity verification, potentially facilitating illegal activities.
The stories of Liz Shelby, Marvis Herring, and countless other victims serve as a cautionary tale for anyone using digital payment apps.
As the popularity of such platforms grows, so does the risk of falling prey to cybercriminals. The onus falls on users and service providers to take adequate measures to ensure a secure and protected digital payment ecosystem.
Exercise caution while making transactions to protect yourself from such scams and fraud. Avoid sharing sensitive information like OTPs, passwords, or personal details over the phone or via messages. Double-check the authenticity of any offers or requests you receive, and be cautious when dealing with unknown individuals.
Peer-to-peer payment apps have undoubtedly simplified our lives, but it’s crucial to remain vigilant and take necessary precautions to avoid falling victim to scams and fraudulent schemes.
India’s digital duel against hackers
India, being one of the biggest countries with the largest number of online payment app users, is especially targeted by hackers.
Due to the sophistication of security and government intervention, most payment apps are secure in India with multi-factor authentication and other layers of security protocol.
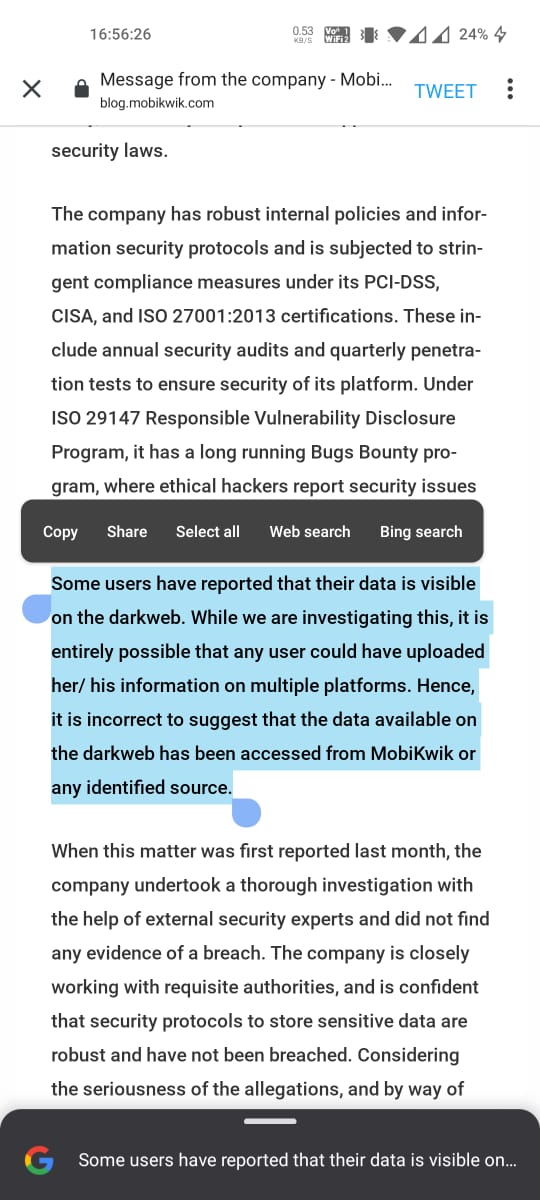
Despite boasting an impressive security structure, numerous payment apps have encountered significant issues, leading to disruption of services and discomfort for millions of users. In one of these incidents, MobiKwik, one of India’s leading digital payments operators, faced a massive data breach that shook the country’s cybersecurity landscape.
Though India has faced many cyber attacks — from companies and startups to government entities — this incident marks one of the biggest digital blows to the Indian payment app security systems.
According to the dark web claims, the attackers behind the MobiKwik data breach possessed 8.2 terabytes of user data.
The platform, which boasts over 120 million users who rely on it for a wide range of transactions, went through a hell-like situation because this data can be used to target victims on a very large scale — as big as taking down an entire nation and creating havoc among citizens.
The compromised data included phone numbers, email addresses, transaction logs, signatures, partial payment card numbers, scrambled passwords, and even personal identification documents, affecting approximately 100 million users.
This extensive trove of sensitive information was available for sale in a searchable database, with a staggering asking price of 1.5 bitcoins, equivalent to around $88,000.
India’s call for enhanced cybersecurity measures

The MobiKwik breach is undoubtedly one of India’s most significant data breaches, but regrettably, it is far from an isolated incident.
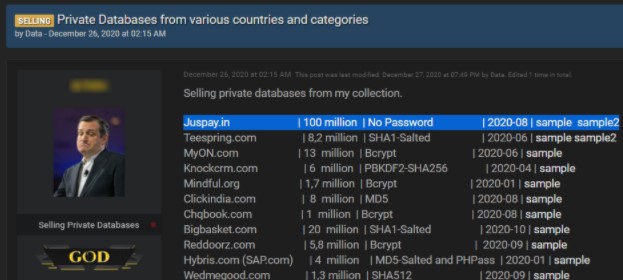
The list of data breaches and cyberattacks is distressingly long.
Similarly, Juspay, a popular payment platform, experienced a data leak compromising over 100 million users’ debit and credit card details.
Late last year, personal information, including names, email addresses, password hashes, contact numbers, and addresses of 20 million customers from the online grocery store BigBasket, was put up for sale on the dark web.
During the first quarter of 2023, India encountered a surge in cyber attacks, experiencing an alarming 18% increase in weekly incidents compared to the previous year.
According to a report by Check Point Research (CPR), each organization in the country had to fend off an average of 2,108 attacks per week.
On a global scale, cyber attacks also rose by 7% in the same quarter, with organizations worldwide facing an average of 1,248 attacks per week.
Among the sectors, the education/research domain suffered the most, enduring an average of 2,507 attacks per organization per week, marking a worrisome 15% increase from the previous year.
The government’s push for cashless transactions has led to a proliferation of payment platforms, mobile wallets, and other consumer software, making digital payments more convenient and widely accessible.
Simultaneously, the Indian government’s push for the Aadhaar digital ID system, a biometric identification system linked to a citizen’s fingerprints and retinal scans, has further amplified the risks.
The Aadhaar database, despite its sensitive nature, remains largely unregulated and unsecured, adding to the potential risks for over 1 billion Indians whose data is linked to it.
India has been grappling with a series of cyberattacks and data breaches for years, yet the urgency to prioritize the digital safety of its growing online consumer base remains alarmingly low. Prioritizing cybersecurity is essential for safeguarding user data and protecting the nation’s digital ecosystem.




















































