In the tender tapestry of innocence, children stand as fragile blossoms, each petal holding dreams, vulnerabilities, and hopes yet to unfold. Yet, this very innocence is looked upon as an opportunity by hackers, who often try to attack the most vulnerable.
The situation takes a more serious turn when vital and sensitive information falls into the hands of these wrongdoers. Such a scenario was recently witnessed at the West Oaks School, where the LockBit ransomware group targeted the school dedicated to children with special needs.
Nestled in Leeds, England, West Oaks School holds a distinctive role, specializing in providing education to children facing an array of challenges. These include conditions such as disabilities, multiple complexities, as well as conditions on the autism spectrum and severe learning impediments.
However, this is not an isolated attack, highlighting the urgency to protect and safeguard student data. It is important to understand the consequences of student data leaks and why it is crucial to protect students, especially those with special needs, at all costs.
Targeting schools and repercussions of student data leaks
In recent past, hackers have launched massive cyber attacks which has led to a spike of over 50% attacks on schools. But how does it affect students when hackers blatantly publish names, numbers, and emails among other details on the dark web?
Information from student data leaks is used to create emails with malicious links which they may click to either give access to their device or have hackers find other information.

This becomes more critical when medical data of students with a learning difficulty or special needs gets available to hackers online.
The following concerns emerge from a student data breach following a cyber attack on a school, especially those dedicated to teaching children with special needs–
- Hackers can talk to students directly by creating emails with identifiable and verifiable information.
- Hackers can ask for more data about them in the name of a survey, financial scheme, a lottery, perks like a game hack, etc.
- Students who have bank accounts can unknowingly click on information-stealing malware sent in emails and other platforms that lead to bank detail leaks.
- Students who find their classmate’s sensitive information online can bully them leading to harassment and other dire consequences.
However, it is important to note that merely the awareness that their health records are accessible online can cause stress, anxiety, and fear in facing others. Student data hacking impacts children who are young and vulnerable and so they need to be approached sensitively keeping their mental and emotional state in mind.
While hackers are finding new ways to cause trauma to targets and extort money, organizations may not be fully equipped to thwart cyber attacks.
Student data leaks and the evolving cybercriminal tactics
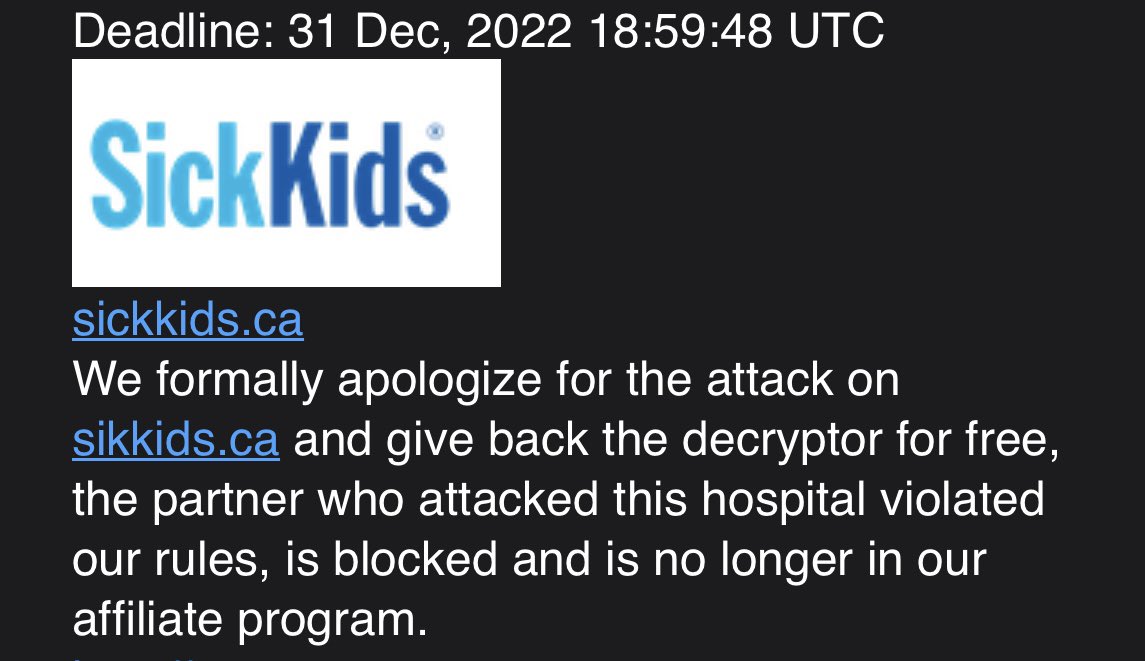
For a ransomware attack on SickKids in December 2022, LockBit hackers apologized for a partner who targeted Canada’s largest chidren’s hospital and encrypted the student data. They offered free decryptors so the data is accessible again and blocked the partner.
Yet, after a few months, LockBit claimed a cyber attack on a school for students with special needs. The Minneapolis Public Schools cyber attack by LockBit shows the vague nature of cybercriminals who on one hand apologize for a cyber attack citing reasons that can be seen on another incident publicly owned by them.
Impact of student data leak on others
A student data leak from a school for the partially able impacts both the students and their parents. Parents and guardians take on the task of teaching their ward while keeping their learning difficulty in mind.
Learning about a data of one’s child can be devastating causing them trauma and stress because not all families prefer to talk openly about their child’s special needs. A student data leak can destroy privacy of the pupil and the parents leaving the data exposed to be misused by miscreants on the dark web.
Friends of the targeted students may see them differently after learning about them through cybercrime further scarring the child emotionally. Most schools have been functioning with minimum cybersecurity tools because of the focus on imparting education, leaving student data vulnerable. It would help if systems are updated, ditching legacy devices.
Transforming student data protection with the K-12 cybersecurity initiative
Considering the missing cybersecurity in schools, it is necessary to secure its infrastructure to fight against cyber crime and data theft. This was addressed in a school cybersecurity initiative published in a statement by the White House that announced funding, training and solutions from various cybersecurity organizations.
Inititiatives such as the recent one taken by the Bidden-Harris administration creates a precedent for others to follow in the direction of cybersecurity for schools.
With the K-12 initiative for U.S. schools, organizations can heave a sign of relief seeing help for teacher training and threat reporting.
It is necessary that governments, educators, and cybersecurity firms collaboratively tackle not just cybercrime but also other problems like offering care to students who suffer naming and shaming by hackers.
Schools must make use of existing government schemes and push for better initiatives to handle data leaks sensitively and proactively. They must gain understanding of projects that offer training about software upgrades, identifying threats, and securing systems.
The White House announced funding, training, and solutions for schools to defend against rising cyber threats.
Accepting cybersecurity as a culture
Cybersecurity and threat landscape are ever-changing however, most cyber crimes are successful due to human error. Inculcating cybersecurity as part of our culture would do more good keeping the present threat scenario in mind. Teenage hackers take law in their hands in the name of hacktivism, or for the sake of making money and pose a grave threat to data privacy.
All while cybersecurity is still an understaffed industry. While training will help in understanding cyber attacks, it is essential to adopt cybersecurity as a culture. This will help in being cognizant of data security at all times regardless of it being student data that one is posting or handling or any other.
It would help if cybersecurity is taught to kids as part of the school syllabus and parents encourage their children to learn about and practice cyber hygiene.
Working as a team and seeking help with cybersecurity
Student data leaks can be heartbreaking and further emotional stress in children with learning difficulties. It is essential on the part of parents, educators, organizations, and governments across the globe to take cybersecurity in schools to the next level.
This can be done with seminars and meetings to address questions about threats, and cybercrime. Parents look up online for information while teachers try to complete the task of teaching. There needs to be a team in every school that addresses the questions of guardians and offers solutions to those who are in doubt.
Students’ data can be protected when students know how to differentiate between phishing emails and genuine communications from people. Not just students, but even parents need to be trained to keep their social media data sharing limited to known contacts.
Student data leak impacts not just the reputation of a student, but the family and the organization. This must be addressed by a team of trained individuals who can help students with special needs and offer holistic help to them.
Even if a hacker gets away with a data leak impacting students with special needs, the targeted educational institution, staff, guardians, and students can work together sportingly. This will create a sense of oneness among the targeted people, and enable them to stand against paying a ransom.



















































