Qualcomm has released the latest security advisory for multiple vulnerabilities. Among them, a Qualcomm vulnerability, designated as CVE-2024-43047, has brought to light concerns surrounding the safety of devices utilizing Qualcomm’s Digital Signal Processor (DSP).
The CVE-2024-43047 refers to a specific security flaw identified in Qualcomm’s DSP architecture, integral to numerous devices, including smartphones, tablets, and IoT gadgets. This vulnerability could allow malicious actors to exploit the DSP, potentially gaining unauthorized access to sensitive data or even executing arbitrary code.
Qualcomm’s DSP is designed to handle various tasks, such as audio processing, image enhancement, and machine learning functions. The versatility of this component makes it a critical aspect of many modern devices. However, this very utility also increases the risk associated with any vulnerabilities in its architecture.
Uncovering the Qualcomm Vulnerability
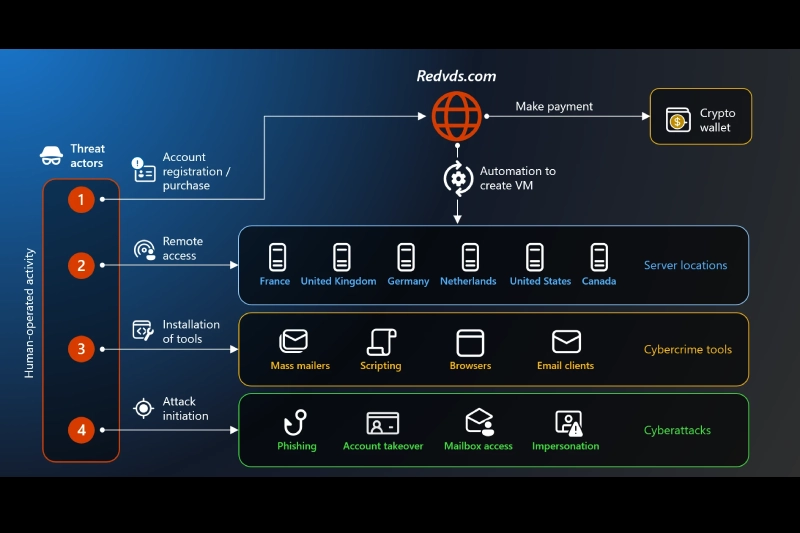
CVE-2024-43047 emerged from ongoing security assessments and research efforts within the cybersecurity community. Experts noted that the vulnerability could potentially enable attackers to escalate privileges on devices running affected versions of the Qualcomm DSP. With devices ranging from high-end smartphones to lower-cost options all potentially at risk, the scope of this vulnerability in Qualcomm is broad and concerning.
As security researchers analyzed deeper into the vulnerability, they found that the impact of this flaw could extend beyond individual devices. If exploited, it could allow attackers to manipulate system-level functions or intercept sensitive communications, leading to data breaches and privacy violations.
The technical specifics surrounding CVE-2024-43047 highlight the complexity of the vulnerability. It is rooted in improper input validation within the DSP’s firmware. This flaw could be triggered through crafted inputs sent to the DSP, leading to memory corruption and the potential execution of malicious code. This chain of events underscores the necessity for better security measures in firmware design and implementation.
To better understand the implications of this Qualcomm vulnerability, it’s essential to consider how DSPs operate. They function by processing data streams in real time, and any compromise in their integrity can have cascading effects throughout a device’s system. The interconnected nature of modern hardware means that vulnerabilities in a single component can expose entire ecosystems to risk.
Responses from Qualcomm and Industry
Upon the identification of CVE-2024-43047, Qualcomm promptly initiated measures to address the issue. The company released security patches aimed at mitigating the risk associated with the vulnerability in Qualcomm’s DSP. Users of affected devices are urged to update their software to the latest versions to ensure they are protected against potential exploits.
Qualcomm’s response included a comprehensive assessment of their current products to determine the extent of the vulnerability’s impact. They have also collaborated with manufacturers and stakeholders to ensure that the patches are rolled out effectively. This proactive approach highlights the importance of swift action in the face of emerging security threats.
While CVE-2024-43047 is a specific instance, it is part of a larger trend involving vulnerabilities in Digital Signal Processors. As these components become more sophisticated, they also present more complex attack vectors for malicious actors. The increasing integration of DSPs in various devices—from autonomous vehicles to smart home technologies—demands heightened attention to their security.
The prevalence of vulnerabilities in Qualcomm’s DSP architecture raises questions about the overall security protocols within the industry. Many manufacturers rely heavily on third-party components, like those from Qualcomm, which can introduce additional risks. The shared responsibility for device security necessitates collaboration between hardware manufacturers, software developers, and cybersecurity experts.
User Awareness and Best Practices
Considering CVE-2024-43047 and similar vulnerabilities, user awareness becomes crucial. Here are several best practices individuals and organizations can adopt to enhance their security posture:
- Keeping devices updated with the latest firmware and security patches is essential. Users should enable automatic updates whenever possible to ensure they receive critical patches promptly.
- Staying informed about known vulnerabilities in devices and understanding the risks associated with them can help users make better security decisions.
- Employing reputable security software can provide an additional layer of protection against potential exploits.
- Users should review app permissions and limit access to sensitive functions, especially in cases where the application interacts with the DSP.
- Participating in discussions within cybersecurity forums can provide insights into emerging threats and effective mitigation strategies.
The Future of Digital Signal Processor Security
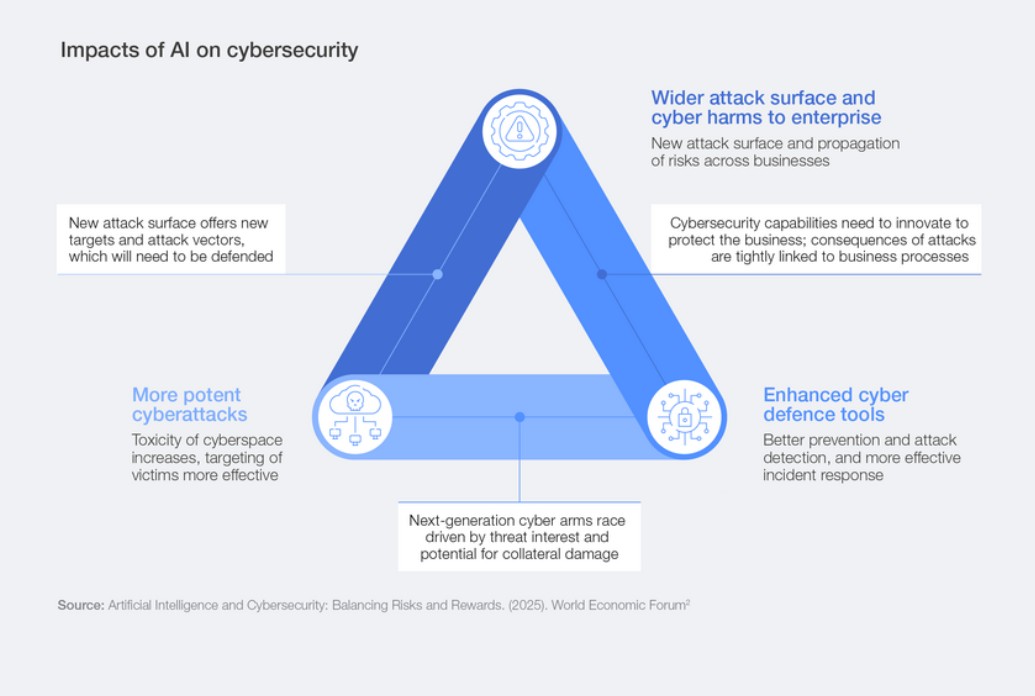
As technologies advance, so will the methods employed by cybercriminals. The ongoing development of machine learning and artificial intelligence tools will shape the nature of DSP vulnerabilities, demanding a robust response from manufacturers and developers.
Qualcomm, along with its competitors, will need to prioritize security in the design phase of their products. Implementing comprehensive security measures, including rigorous testing for vulnerabilities, will be vital in protecting users from potential exploitations. Furthermore, industry-wide standards for firmware security and vulnerability disclosure will help create a more secure environment for consumers.