Innefu Labs, an Indian cybersecurity firm known for its advanced AI and data analytics solutions, has reportedly fallen victim to a sophisticated cyberattack. This narrative unfolds in the backdrop of similar incidents targeting Indian cybersecurity firms setting a foreboding tone for the story.
The Innefu Labs breach is not just a blow to the company, with its annual revenue exceeding $25 million, but also to its wide array of clients, including corporate and government sectors.
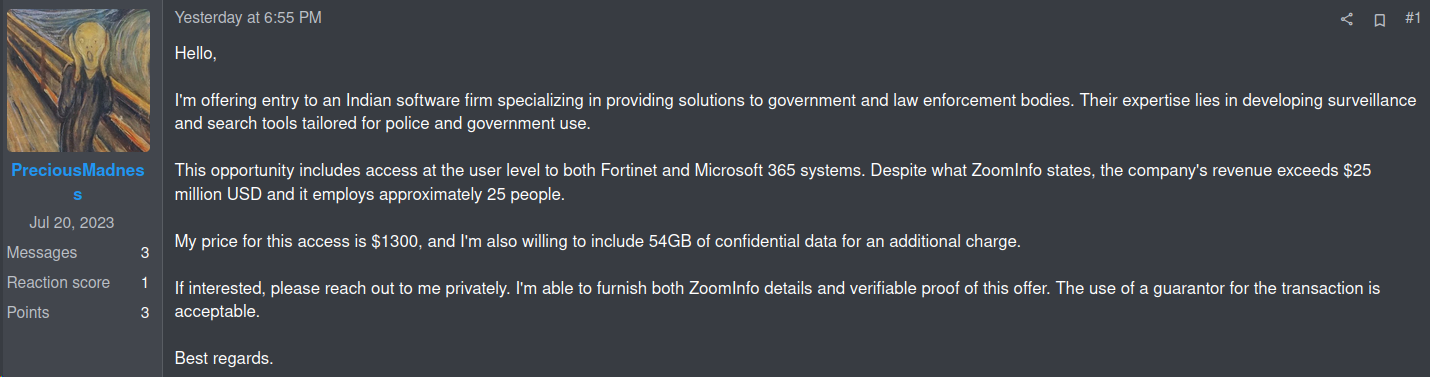
On January 10, 2024, a threat actor identified as ‘PreciousMadness’ announced on the RAMP forum their possession of unauthorized access to Innefu’s systems.
Founded in 2012 by Tarun Wig and Abhishek Sharma, Innefu Labs offers products for identity authentication, predictive intelligence, and data protection to various corporate and government clients.
The Innefu Labs data breach has caused quite a stir in the cybersecurity sector, drawing attention to the vulnerabilities even within the firms specializing in digital security.
The Cyber Express team has contacted Innefu Labs for an official statement to verify the details of the reported data breach. However, the firm has failed to respond to our queries.
Innefu Labs Data Breach: What We Know So Far?
PreciousMadness’s offering includes unauthorized access to crucial components of Innefu’s infrastructure, such as Fortinet VPN and Microsoft 365 Services, priced at USD 1,300. Moreover, the Innefu data breach involves 54 GB of exfiltrated data, available for an additional cost.
The threat actor has encouraged potential buyers to contact privately for proofs and more details, a standard practice in such underground forums.
Adding to the gravity of the situation, the threat actor has also advertised the same unauthorized access on other platforms like XSS and Exploit Forums. This suggests a deliberate and widespread attempt to capitalize on the compromised security of Innefu Labs, highlighting the seriousness of the breach.
The Innefu cyberattack not only impacts India but has broader implications for the Asia and Pacific (APAC) region. It raises stark concerns about the state of cybersecurity and the resilience of even the most adept firms against sophisticated cyber threats.
Innefu Labs, now faces the challenge of addressing this breach and reinforcing its defenses against future threats, a task that is increasingly becoming vital for all players in the space.
An investigation done by The Cyber Express with the help of multiple independent researchers, has revealed that the data breach at Innefu Labs has led to the exposure of sensitive information belonging to various Indian and overseas entities. This includes individuals, major conglomerates, politicians, and even agencies of the Indian government.
This breach has potential and significant national security implications, as it exposes sensitive information that could potentially be exploited. Moreover, Innefu Lab data breach’s impact is not confined to India alone; it has broader implications for the entire Asia & Pacific (APAC) region.
To gain a comprehensive understanding of the situation, The Cyber Express engaged with various researchers and contacted Cyble Research and Intelligence Labs (CRIL) for their perspective on the security breach.
CRIL acknowledged the gravity of the situation but chose not to disclose further information, citing the sensitive and confidential nature of the data involved.
“CRIL is aware of the seriousness of the recent security breach. However, due to the sensitivity of the entities involved, the extent of the nature of the information, and the significant scale of the data, we are unable to provide further details or comment at this time,” it said.
Surveillance and Privacy Concerns
Innefu Labs’ involvement in surveillance technologies has been a subject of public debate, particularly following an RTI request by Anushka Jain of IFF. This request raised important questions about the use of Automated Facial Recognition System (AFRS) technology by Delhi Police, which was sourced from Innefu Labs.
The response from the Delhi Police, invoking the RTI Act, to withhold information under the pretext of “commercial confidence, trade secrets, or intellectual property,” had sparked concerns about transparency and accountability in the use of surveillance technologies.
News18 reached out to Tarun Wig of Innefu Labs to address the concern of “commercial confidence, trade secrets or intellectual property”. In response, Wig had stated, “The technology, its servers and applications are entirely within their (Delhi Police’s) premises, and our role is only limited to occasional server maintenance, as per their requirements.”
Talking about upon Innefu’s contractual agreement of service with the Delhi Police, Wig said, “If the Delhi Police have such a thought process (of treating AFRS as a trade secret), that would be their internal decision. They may wish to refrain from revealing the technical details behind such technologies in order to prevent other private entities from using it. Personally, I am not aware of any clause or contract that binds them to it.”
Innefu’s Role in Global Cybersecurity and Surveillance
The story of Innefu Labs intertwines with another shadowy figure in the cyber world – the Donot Team, also known as APT-C-35 and SectorE02. An investigation by Amnesty International had revealed potential connections between the Indian cybersecurity company, and spyware attacks targeting a notable human rights advocate in Togo.
This Togolese individual in question was the focus of cyberattacks involving spyware, previously associated with the Donot Team, during the politically turbulent period of late 2019 and early 2020. The attempts to infiltrate the activist’s Android and Windows devices using this spyware were, however, unsuccessful.
The Donot Team, a name coined by researchers to describe the cyber threat actors initially identified in South Asia through a 2018 Netscout research, has been linked to various attacks across Asia, particularly in northern India, Pakistan, and Kashmir.
While Amnesty International’s report does not directly accuse Innefu Labs of being involved in the attacks on the Togolese activist, it does highlight digital forensic evidence, including IP addresses, that suggest a connection between the company and the spyware tools used.
The report states, “The technical evidence suggests that Innefu Labs is involved in the development or deployment of some Donot Team spyware tools.”
In response to these allegations, Innefu Labs categorically denied any involvement. In a statement dated October 1, 2021, included in the report, the company asserted, “We firmly deny the existence of any link whatsoever between Innefu Labs and the spyware tools associated with the ‘Donot Team’ group and the attacks against a Human Rights Defender in Togo.”
This connection paints a complex picture of Innefu Labs, not just as a victim of the Innefu Data Breach but also as a player in the controversial field of surveillance technology.
Cyberattacks Targeting Indian Cybersecurity Firms
The Innefu Labs data breach, in many ways, mirrors the earlier CloudSEK data breach. In 2022, CloudSEK faced a cyberattack where the compromise of an employee’s Jira password, led to unauthorized access to their Confluence pages.
During this breach, the attacker was able to view internal content such as screenshots, bug reports, customer identities, and schema diagrams. Fortunately, the attack did not extend to database or server breaches. In response, the cybersecurity company launched an investigation and kept the public informed through a blog.
The trend of cyberattacks against Indian cybersecurity companies, epitomized by these high-profile breaches, signals a concerning shift in the landscape of digital security.
These incidents are not isolated events but rather indicative of a broader, more systemic challenge facing the cybersecurity sector in India and globally.
Firstly, these attacks underscore the paradox that even those organizations tasked with safeguarding digital assets are not immune to the very threats they combat.
The sophistication and success of the Innefu Labs data breach reveal that attackers are becoming increasingly adept, often outpacing the defensive mechanisms in place. This escalation demands a re-evaluation of current security strategies within the cybersecurity industry, emphasizing the need for continuous innovation and adaptation in defense tactics.
Moreover, the trend highlights a crucial vulnerability in the cybersecurity infrastructure of a country that is rapidly digitizing. As India continues to embrace digital transformation across various sectors, the security of data and systems becomes paramount.
The breaches at Indian cybersecurity companies serve as a stark reminder of the potential consequences of cybersecurity lapses, not just for the companies involved but for the broader ecosystem, including government agencies, financial institutions, and private citizens.
Innefu Labs data breach also raise important questions about the ethical responsibilities of cybersecurity firms, especially when dealing with sensitive surveillance technologies. The balance between providing advanced security solutions and ensuring the ethical use of such technologies is delicate and complex.
The involvement of Indian cybersecurity firms in controversies related to surveillance and data scrapping adds another layer of concern, highlighting the need for robust ethical guidelines and oversight in the industry.