Healthcare data breaches have surged over the years, with the number of reported incidents nearly doubling from 329 in 2016 to 739 in 2023. This sharp rise shows the critical need for strong healthcare data protection strategies, as breaches in 2023 alone compromised over 136 million individual records—more than double the previous year’s total.
In response to this growing threat, the role of Chief Information Security Officers (CISOs) in healthcare has become increasingly vital. CISOs are tasked with safeguarding sensitive patient data and implementing comprehensive defense mechanisms. One of the key tools in their arsenal is CISO take down services for healthcare, which are essential in mitigating the impact of data breaches and ensuring the integrity of healthcare information.
This article delves into the strategies CISOs use to protect healthcare data, with a particular focus on how they deploy take down services to enhance security and respond to breaches effectively.
Healthcare Data Protection Strategies
Healthcare data protection strategies are essential in today’s digital age, where healthcare organizations rapidly collect and store vast amounts of sensitive patient information. The sheer volume of data being handled makes safeguarding it a complex and challenging task. With every piece of data collected, the risk of healthcare data breaches increases, and the consequences of these breaches can be devastating.
Not only can they tarnish an organization’s reputation, but they can also lead to significant financial losses, especially with penalties for violations like HIPAA reaching up to $1.5 million annually.
Given that hospitals alone account for 30% of all large data breaches, it is crucial for healthcare providers to continuously upgrade their security measures. A enhanced healthcare data protection strategy must encompass a variety of approaches, from implementing advanced encryption technologies to ensuring strict access controls. However, technology alone isn’t enough.
A crucial, often overlooked, aspect of data protection is staff training. With human error responsible for 74% of all data breaches, educating employees on best practices and fostering a culture of security awareness is a vital component of any effective strategy.
Ultimately, protecting healthcare data is not just about complying with regulations—it’s about safeguarding the trust and well-being of patients.
CISO Take Down Services for Healthcare
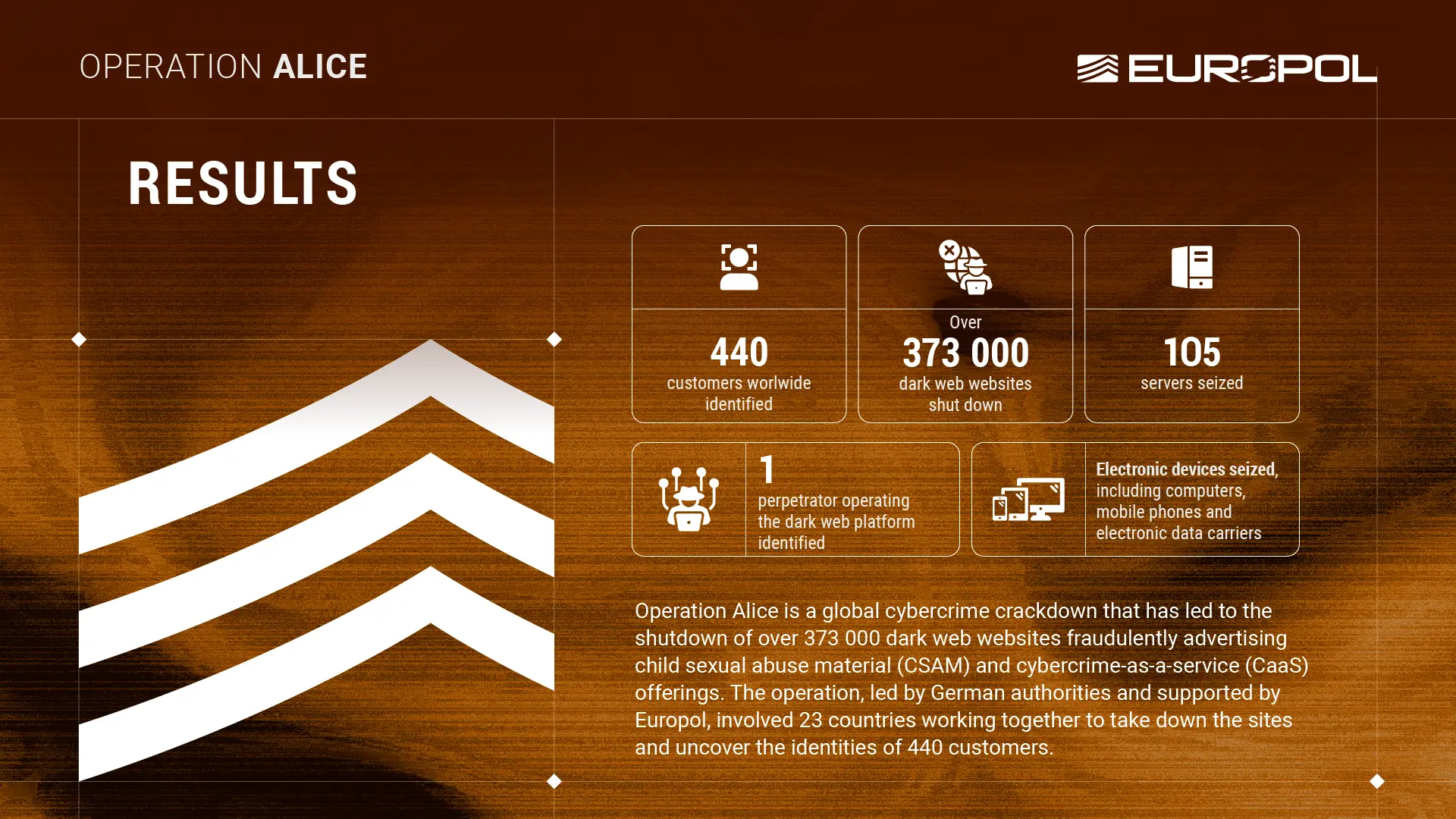
Building on the critical role of CISOs in safeguarding healthcare data, CISO take down services for Healthcare emerge as a pivotal component in the fight against healthcare data breaches. But what exactly are these services? In essence, take down services involve the identification and removal of unauthorized or harmful data—whether it’s exposed patient information, counterfeit websites, or phishing content—from the internet.
These services work by swiftly tracking down and eliminating threats that could compromise sensitive healthcare data, thereby preventing further exploitation by cybercriminals.
In the healthcare sector, where the stakes are incredibly high, CISOs leverage these take down services as a frontline defense mechanism. For instance, if a healthcare organization experiences a data breach, a data breach response healthcare CISO will quickly activate take down services to identify where the stolen data has been posted—whether on the dark web or rogue websites—and ensure its immediate removal. This rapid response is crucial in mitigating the damage caused by a breach and protecting patients’ sensitive information.
A prime example of this in action can be seen when a hospital’s patient database is leaked online. The CISO, recognizing the imminent threat, would deploy healthcare data security take down solutions to trace the leak, coordinate with internet service providers and law enforcement, and ensure that the data is removed before it can be misused. This proactive approach not only curbs the potential fallout but also demonstrates the effectiveness of take down services as a vital tool in the healthcare cybersecurity arsenal.
These services are not just reactive but also preventative. By regularly monitoring the internet for signs of leaked data or phishing schemes targeting the organization, CISOs can preemptively strike against threats before they escalate into full-blown breaches. This ongoing vigilance is what keeps healthcare data safe in an increasingly perilous digital landscape, making CISO take down services for healthcare an indispensable aspect of modern healthcare data protection strategies.
Data Breach Response for Healthcare CISOs
When a healthcare data breach is detected, the immediate response from CISOs is crucial in containing the damage and protecting sensitive information. The first step is swift action—CISOs must quickly mobilize their teams to secure systems, isolate the breach, and begin an in-depth investigation. This rapid response is the foundation of effective data breach response for healthcare CISOs, as it minimizes the potential fallout from the incident.
One of the most powerful tools in a CISO’s arsenal during this critical time is the use of take down services for healthcare. These specialized services are designed to remove malicious content or stolen data from the web as quickly as possible. Whether it’s patient records, proprietary research, or other sensitive data, these take down solutions are essential for preventing further exposure and misuse. By coordinating closely with take down service providers, CISOs can ensure that any leaked information is swiftly eradicated from public access, significantly reducing the breach’s impact.
Once the immediate threat is contained and take down services have done their work, the focus shifts to post-breach analysis. This involves a thorough examination of how the breach occurred, what vulnerabilities were exploited, and how future incidents can be prevented.
Healthcare data security take down solutions play a pivotal role here as well, offering insights into the breach’s dynamics and helping to fortify defenses against similar attacks in the future. By continuously refining their strategies based on these learnings, CISOs can enhance their organizations’ resilience and ensure stronger protection of healthcare data moving forward.
Healthcare Cybersecurity Best Practices
Healthcare cybersecurity best practices are crucial in a sector where the stakes are incredibly high—patient data security isn’t just a regulatory requirement; it’s a matter of trust and safety. With cybercriminals constantly seeking to exploit vulnerabilities for financial gain, healthcare organizations must stay ahead of the curve. These criminals use sophisticated methods, including fake social media accounts and rogue mobile apps, to trick users and gain unauthorized access to sensitive information.
To combat these threats, it’s essential for healthcare providers to adopt a proactive approach to cybersecurity.
One of the most effective healthcare cybersecurity best practices is continuous monitoring and assessment of potential risks. This involves not just reacting to threats but anticipating them. By identifying vulnerabilities before they can be exploited, healthcare organizations can prevent data breaches before they happen. Companies like Cyble play a critical role in this proactive defense, offering solutions that help healthcare providers stay one step ahead of cybercriminals.
Another key practice is ensuring that all systems and software are regularly updated and patched. Outdated systems are a common entry point for hackers, making it imperative that healthcare organizations maintain up-to-date defenses. Employee training is also a cornerstone of healthcare cybersecurity best practices. Ensuring that all staff members, from doctors to administrative personnel, are aware of the latest threats and know how to respond to them can drastically reduce the likelihood of a successful cyberattack.
Finally, having an enhanced incident response plan is vital. Despite the best preventive measures, breaches can still occur, and when they do, the speed and effectiveness of the response can make all the difference.
Healthcare organizations must have a clear plan in place, ensuring that they can quickly contain any breach and minimize its impact on patient data security. By embracing these best practices, healthcare providers can protect their patients and maintain the trust that is so essential to their mission.
Explore how Cyble can assist in cybersecurity for healthcare and ensure a comprehensive approach to third-party risk management in healthcare.