In the wake of the recent cyberattack that shook Fulton County, the aftermath lingers, touching lives in unexpected ways. For folks like Zack, who call Fulton County home, the fallout has been more than just a news headline. Fulton County cyberattack has become a personal battle, impacting their everyday routines and, in Zack’s case, his ability to make ends meet.
As he tried to carry on with his life in Seattle, working for a rideshare company, the sudden failure of his background check threw everything into disarray. Now, uncertainty looms large, and the strain on both his wallet and his peace of mind is palpable.
And he’s not alone. Countless others are navigating similar challenges in the aftermath of the Fulton County cyberattack.
Fulton County Cyberattack Continues to Affect the Residents
Jasmine shared her distressing experience with 11Alive, explaining how the cyberattack on Fulton County has jeopardized her job prospects and forced her into the unsettling reality of facing homelessness. Unable to start the job she was hired for, Jasmine finds herself in a precarious situation, uncertain of what the future holds.
The impact extends beyond individuals, with third-party background checks requiring review of police report records experiencing delays and complications. The county acknowledges the challenges, noting that efforts to restore affected systems are underway. However, the timeline for resolution remains uncertain, leaving many in a state of limbo and anxiety.
Amidst the chaos, there are glimmers of progress, with several systems gradually coming back online. The county reassures residents that restoration efforts are ongoing, with more systems expected to be operational soon. However, the road to recovery is met with challenges, and the community remains on edge, awaiting clarity and resolution.
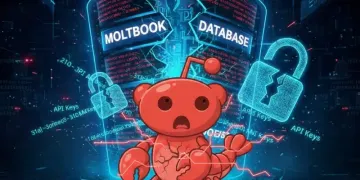
LockBit Ransomware Group Claimed the Fulton County Cyberattack
This Fulton County cyberattack was previously claimed by the now-banned LockBit ransomware group. In February 2024, Fulton County found itself at the hands of hackers who disrupted government services, including office phone lines and the issuance of vital documents like vehicle registrations and marriage licenses.

The hackers, identified as the LockBit ransomware group, threatened to release stolen data, including sensitive personal information if their demands were not met. The threat actor also opted for a timer on their dark web post, stating Fulton County has 1 day and 23 hours before the data gets leaked.
Additionally, the threat actor claimed attacks on multiple organizations on February 14, 2024, including Universal Services LLC, Rajawali Corpora, Caribbean Radiation Oncology Center, MMI Culinary and lastly the cyberattack on Fulton County government,
Despite efforts by law enforcement agencies to disrupt LockBit’s operations and apprehend individuals associated with the group, the threat persists, leaving communities vulnerable to future attacks.
Stories of Resilience and Recovery
As the community grapples with the aftermath of the Fulton County cyberattack, it’s evident that this isn’t just a distant news story—it’s a human crisis. Zack, Jasmine, and countless others are facing real hardships, from disrupted livelihoods to uncertain futures.
Yet, amidst the chaos, there’s resilience and hope. Despite the challenges, efforts to restore systems are underway, and gradual progress is being made. However, the journey to full recovery is far from over, and the community’s patience and perseverance will be crucial in the days ahead.
As we navigate these uncertain times together, let’s remember the strength we find in unity and support. Whether it’s lending a helping hand to those in need or advocating for stronger cybersecurity measures, each of us has a role to play in rebuilding and safeguarding our community against future threats.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.