Frontier Communications, a prominent telecom provider in the United States, finds itself grappling with the aftermath of a recent cyberattack orchestrated by a nefarious cybercrime group. The cyberattack on Frontier Communications, which occurred on April 14, 2024, has thrown the company into disarray as it races to restore its compromised systems and reassure its millions of customers across 25 states.
The cyberattack on Frontier Communications, detected by the company’s vigilant cybersecurity team, prompted the company to take swift action, partially shutting down affected systems to thwart further unauthorized access.
This proactive measure, while essential for containing the breach, resulted in operational disruptions, leaving many customers facing internet connection issues and encountering difficulties reaching support services.
Disclosure of Cyberattack on Frontier Communications
In a regulatory filing with the U.S. Securities and Exchange Commission (SEC) on Thursday, Frontier Communications divulged the unsettling details of the breach.
The cybercriminals managed to infiltrate portions of the company’s information technology infrastructure, gaining access to sensitive personally identifiable information (PII). While the specifics of the compromised data remain undisclosed, concerns linger regarding the potential exposure of customer and employee information.
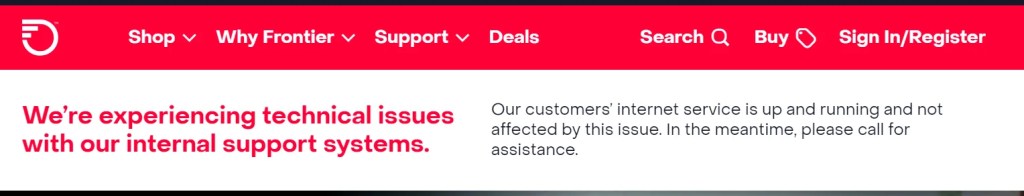
Despite the severity of the cyberattack on Frontier Communications, Company assures stakeholders that it has successfully contained the incident and restored its core IT systems affected during the attack. However, the road to recovery has been fraught with challenges, as evidenced by ongoing technical issues plaguing the company’s website.
Customer Conundrum: Support Snags and Communication Breakdowns
Customers attempting to access Frontier’s online services are met with warnings of internal support technical difficulties, exacerbating frustrations amid the connectivity woes.
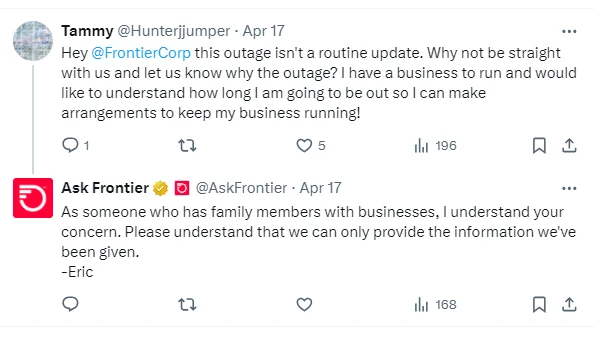
Furthermore, reports have surfaced indicating that affected customers are experiencing prolonged internet outages, with support phone lines inundated with prerecorded messages instead of connecting to live operators.
This breakdown in customer communication compounds the anxiety and uncertainty surrounding the situation, underscoring the urgency for Frontier to swiftly address the fallout from the cyberattack on Frontier Communications.

In response to the breach, Frontier has mobilized a comprehensive investigative effort, enlisting the expertise of cybersecurity specialists and promptly notifying law enforcement authorities.
Despite these concerted efforts, a Frontier spokesperson remained unavailable for comment when contacted by The Cyber Express Team, leaving concerned consumers clamoring for reassurance and transparency from the embattled telecom provider.
Amid the chaos and disruption wrought by the cyberattack, Frontier remains steadfast in its commitment to safeguarding customer data and restoring normal business operations. While the company maintains that the incident is unlikely to have a significant impact on its financial standing, the full extent of the breach’s ramifications is yet to be fully realized.
As stakeholders await further updates from Frontier, the telecom giant faces a critical test of resilience and accountability in the wake of these brazen cyberattacks. Only time will tell whether Frontier can emerge from this trial stronger and more fortified against future threats or if lingering doubts and repercussions will continue to cast a shadow over its operations.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.