Bluewater Health, a prominent hospital network in Ontario, Canada, has fallen victim to an alleged cyberattack, affecting several hospitals, including Windsor Regional Hospital, Erie Shores Healthcare, Chatham-Kent Health, and Hôtel-Dieu Grace Healthcare.
The Bluewater Health cyberattack has been attributed to the notorious Daixin Team hacker group, known for targeting healthcare and public health sectors in the United States.
Details of the Bluewater Health cyberattack
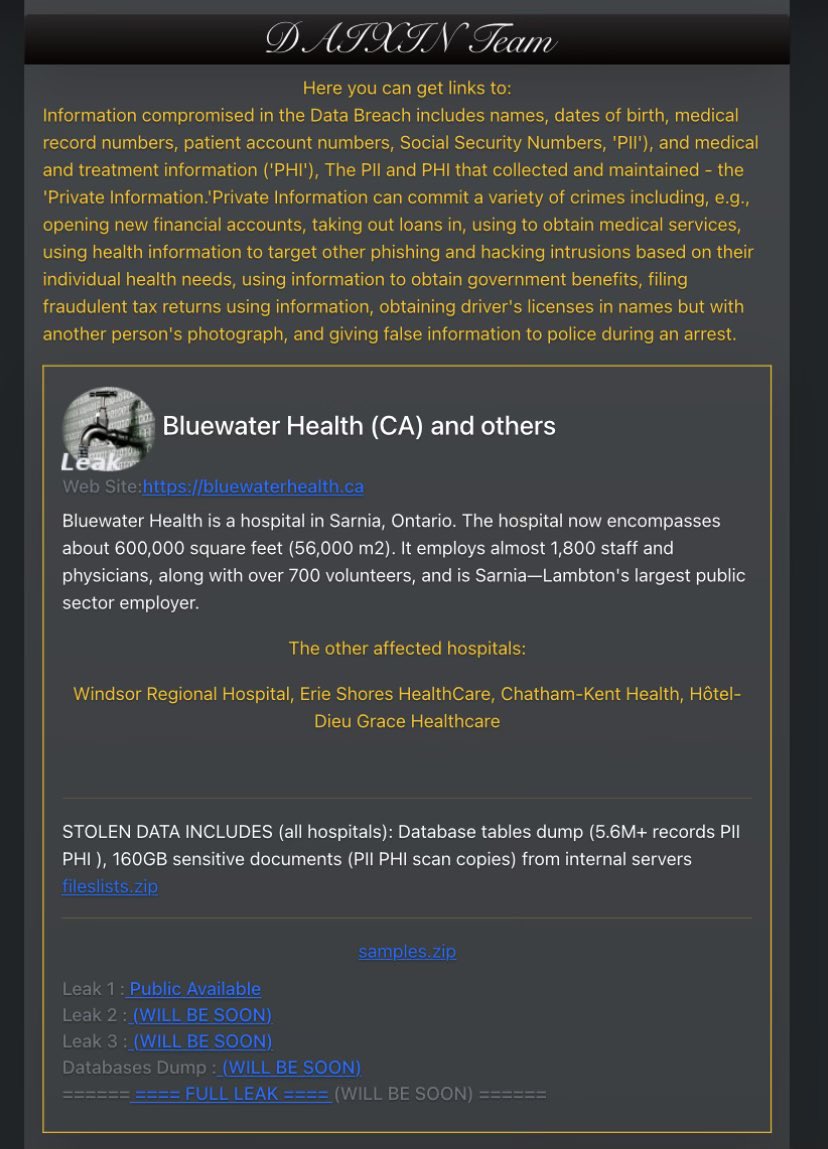
The Daixin Team’s claim of responsibility for the Bluewater Health cyberattack underscores the severity of the incident.
The compromised data includes a range of sensitive information such as names, dates of birth, medical record numbers, patient account numbers, and even Social Security Numbers (SSN), collectively known as Personally Identifiable Information (PII).
Additionally, medical and treatment records, referred to as Protected Health Information (PHI), were also exposed.
The leak of such private information poses a significant threat to affected individuals. PII and PHI can be exploited for various malicious activities, including fraudulent financial transactions, obtaining medical services, and even targeting individuals with phishing and hacking attempts based on their health data.
This Bluewater Health cyberattack could lead to serious repercussions for those affected, ranging from financial loss to potential identity theft.
Bluewater Health cyberattack: List of the Affected Hospitals
Apart from Bluewater Health, several other hospitals have been impacted by this cyberattack. The victims include Windsor Regional Hospital, Erie Shores Healthcare, Chatham-Kent Health, and Hôtel-Dieu Grace Healthcare.
The stolen data encompasses an extensive database dump of over 5.6 million records of PII and PHI, as well as 160GB of sensitive documents, including scanned copies of PII and PHI from internal servers.
In light of this incident, The Cyber Express has made efforts to reach out to Bluewater Health for official confirmation and further details into the Bluewater Health data breach.
However, at present, the hospital’s website is inaccessible, displaying an error message, which has hindered any direct communication. As a result, the claims surrounding the Bluewater Health cyberattack remain unverified.
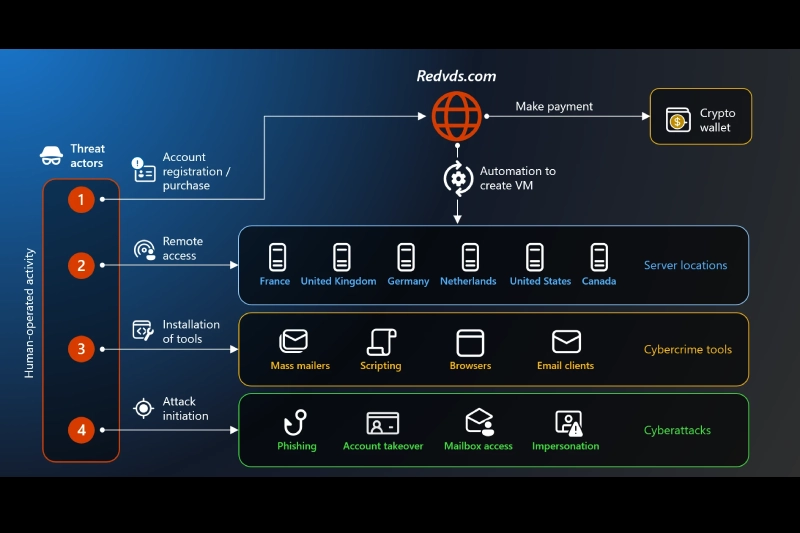
The Daixin Team hacker group is a notorious cybercrime organization known for its aggressive targeting of U.S. businesses, particularly within the Healthcare and Public Health (HPH) sector. According to the FBI Internet Crime Complaint Center (IC3) data from October 2022, the HPH sector accounted for 25 percent of all reported ransomware complaints across critical infrastructure sectors.
The group’s modus operandi involves deploying ransomware to encrypt critical healthcare services and threatening to release sensitive patient information if a ransom is not paid.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.